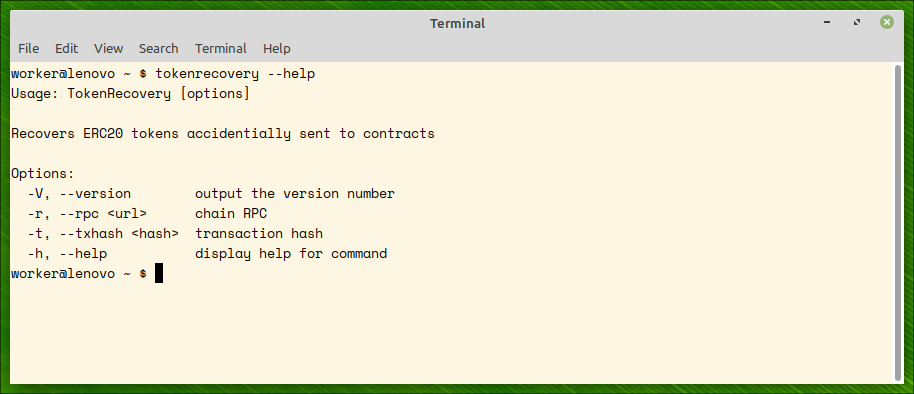
TokenRecovery is a command line utility which tries to recover ERC20 tokens from contract addresses.
Downloads
The code is open source: Github repo
How to use the program: Tutorial
Introduction In the world of cryptocurrencies and blockchain, Ethereum has stood out as a pioneer with its versatile smart contract capabilities. ERC-20 tokens, a popular standard on the Ethereum platform, have enabled the creation of countless tokens that can represent various assets, projects, and utilities. However, amidst the convenience of token transfers, accidents can happen – sending ERC-20 tokens to a contract address instead of a wallet. In this article, we’ll delve into the common predicaments faced by users who have mistakenly sent tokens to a contract address and explore possible solutions for each scenario.
[Read More]
Unlocking the World of Algorithmic Trading on Crypto Exchanges: Strategies, Tools, and Insights
In the fast-paced realm of cryptocurrency markets, where volatility and opportunities abound, algorithmic trading has emerged as a powerful tool for traders seeking to capitalize on market movements with precision and speed. Algorithmic trading, often referred to as algo trading, leverages computer algorithms to execute trades automatically based on pre-defined strategies. In this article, we delve into the world of algorithmic trading on crypto exchanges, exploring the platforms that allow it, how to learn the craft, the essential tools, and the underlying theories that drive success in this dynamic landscape.
[Read More]
Decoding Blockchain Consensus Mechanisms: A Comparative Analysis of Implementation Complexity and Robustness
In the realm of blockchain technology, consensus mechanisms play a pivotal role in maintaining the integrity and security of distributed ledgers. These mechanisms determine how nodes on the network agree on the state of the blockchain and validate transactions. Various consensus algorithms have emerged, each with its own strengths and complexities. In this article, we’ll delve into the most prominent types of blockchain consensus mechanisms—Proof of Work (PoW), Proof of Stake (PoS), Proof of Authority (PoA), and Delegated Proof of Stake (DPoS)—and compare their implementation complexity and robustness against violations and centralization.
[Read More]
Self-Destructing Solidity Contracts: A Closer Look at Smart Contract Termination
In the realm of blockchain and smart contracts, innovation is the driving force that propels the technology forward. One fascinating aspect of Ethereum’s Solidity programming language is the ability to create contracts that can intentionally self-destruct. While this might seem counterintuitive, self-destructing contracts serve specific purposes within the Ethereum ecosystem. In this article, we’ll explore the concept of self-destructuring Solidity contracts, discuss their use cases, and provide a code example to illustrate their implementation.
[Read More]
Predicting Bitcoin Price Fluctuations: The Statistical Frontier
In the dynamic landscape of cryptocurrencies, Bitcoin stands as the beacon that ignited a revolution in the financial world. With its unprecedented volatility and market intricacies, the ability to predict Bitcoin price fluctuations has captured the attention of data scientists and researchers alike. Leveraging the power of statistics, experts are exploring data-driven methodologies to forecast the ebbs and flows of the cryptocurrency’s value. In this article, we delve into how statistics is harnessed to predict Bitcoin price fluctuations and highlight notable articles on this topic available on Sciencedirect.
[Read More]
Defending Against Malicious Miners: The Ingenious Mechanisms of Bitcoin Consensus
In the realm of blockchain technology, where decentralization and security reign supreme, Bitcoin stands as a testament to the power of consensus mechanisms. While the vast majority of miners contribute to the network’s well-being, the possibility of malicious actors attempting to undermine the integrity of the system is an ever-present concern. Bitcoin’s consensus mechanism, built on a foundation of cryptographic principles and game theory, employs a myriad of ingenious mechanisms to thwart the efforts of these malicious miners.
[Read More]
David Chaum: Pioneering Cryptographer and the Vision of Blind Signatures
In the world of cryptography, where secrecy and security dance in delicate balance, one name stands out as a trailblazer: David Chaum. His contributions have not only shaped the field but have also laid the groundwork for the protection of digital privacy. Among his revolutionary inventions, the concept of blind signatures shines as a beacon of ingenuity, reshaping the landscape of cryptographic protocols and digital anonymity.
Early Life and Education David Lee Chaum was born on May 31, 1955, in New York City, USA.
[Read More]
Decoding the Choice: Elliptic Cryptography vs. RSA for the Ethereum Blockchain
In the digital age, cryptography stands as a sentinel, guarding the integrity, privacy, and security of our transactions and communications. As the backbone of modern encryption, cryptographic algorithms such as RSA (Rivest-Shamir-Adleman) and elliptic cryptography play pivotal roles. But when it comes to securing the Ethereum blockchain, it’s the elegance and efficiency of elliptic cryptography that prevails over the traditional RSA algorithm. In this editorial, we explore the differences between these two cryptographic powerhouses and delve into the reasons why elliptic cryptography is the chosen path for the Ethereum network.
[Read More]
Avoiding a Costly Mistake: Sending ERC-20 Tokens to Contract Addresses
The world of cryptocurrency is marked by innovation and opportunity, but it’s also a realm where a single mistake can have significant consequences. Among the various pitfalls that cryptocurrency holders can encounter, one of the most distressing is accidentally sending ERC-20 tokens to a contract address. In this article, we’ll delve into the common misstep of sending tokens to the wrong address and explore the potential solutions to this predicament.
[Read More]
Ensuring Secure Play on Crypto Loko Casino: Navigating the Realm of Safe Gambling
In the dynamic world of online casinos, the emergence of cryptocurrency-based platforms like Crypto Loko Casino brings a new level of excitement and innovation. As players flock to experience the unique offerings of these platforms, ensuring security becomes paramount. In this article, we delve into the essential aspects of security when playing on the Crypto Loko Casino platform.
The Importance of Security in Online Gambling Security is a foundational pillar of any online gambling platform, and Crypto Loko Casino takes this aspect seriously.
[Read More]